Glossary
A collection of acronyms, terms and words compiled for enthusiasts, family, students, teachers and technicians alike. If you consider that you may be able to add to the glossary or have any comments, please complete the 'quick contact' form on the home page.
Jump to
A-Z

802.11 (Broadband)
A group of specifications for wireless networks developed by the Institute of Electrical and Electronics Engineers (IEEE): These are: 802.11, 802.11a, 802.11b, 802.11g, 802.11i and 802.11n… used by the WiFi Alliance (See also: WAN, WEP, WPA).

ADSL (Broadband)
Asymmetric Digital Subscriber Line – ADSL technology turns a conventional copper-pair analogue telephone line into an always-on digital connection with a data speed operating in the region of 160, possibly as much as 480, times faster than the now redundant 56K modem (See also: LLU, PSTN, STD, VDSL).
ADWARE
Advertising supported software (Ad-ware) conceivably installed to your computer by mistake or without consent, causing pop-ups and the like, quite possibly taking unauthorised control of your Internet Browser. Adware is usually seen by the developer as a way to recover development costs, and in some cases may allow the software to be provided free of charge or at a reduced price.
Some types of Adware are invasive, may collect information to pass or sell on to third-parties, and may in turn further impact on limited resource, compound existing issue with your operating system, leading or contributing to instability (Must see also: MALWARE).
AFFECTORS'
Invisible characters – For example a 'Paragraph mark' ¶. Show/Hide on the Standard Toolbar in Word; Show Special Characters in Publisher (View menu (Some versions)).
AI
Artificial Intelligence.
ALIGNED
Text that is aligned to one side (See also: FLUSH, JUSTIFY and/or RANGE).
AMD
Advanced Micro Devices – An American multinational semiconductor company based in Sunnyvale, California, that develops computer processors and related technologies for commercial and consumer markets [1969] (See also: INTEL).
ANPR (Transport)
Automatic Number-Plate Recognition.
API
Application Programming Interface (See also: SAPI).
APPLET (Smart Card)
An application written in the Java™ programming language – The current Visa Smart Credit/Debit (VSDC) applications, as well as increasingly more value-added applications such as loyalty are written in Java™ (See also: JAVA, VSDC).
APPLICATION SOFTWARE
Software application tool specific to the needs of the user – Packages might be, for example, Microsoft Word, Excel, Access, PowerPoint, Works, Publisher, Word Perfect etc.
ARM
Advanced RISC Machine (See also: RASPBERRY Pi, RISC).
ARQC (Smart Card)
Authorisation Request Cryptogram – A cryptogram used for a process called Online Card Authentication. This cryptogram is generated by the card for transactions requiring online authorisation.
It is the result of card, terminal, and transaction data encrypted by a DES key. It is sent to the issuer in the authorisation or full financial request. The issuer validates the ARQC to ensure that the card is authentic and card data was not copied from a skimmed card (See also: DES).
ASCENDER (Typography)
The vertical stem above the x-height in a lower case character set, e.g. b, d and h (See also: DESCENDER).
ASCII
American Standard Code for Information Interchange [1963] (See also: BINARY (digit)).
ATA
Advanced Technology Attachment – P(Parallel)ATA; S(Serial)ATA (See also: IDE).
AUP
Acceptable Use Policy – An organisation's management of employee IT use.

BASE 10
Method – see: DENARY (See also: BINARY (digit)).
BASELINE (Typography)
An invisible line that string of characters rest on (See also: LINE SPACING).
BASELINE (Configuration Management)
A system restore-point created following a new installation, conceivably allowing the system administrator/user to restore their computer to a pre-configured stable platform.
BASIC (Programming)
Beginner's All-Purpose Symbolic Code.
BBS (Internet)
Bulletin Board System (See also: DCC, IRC).
BCD
Binary-coded decimal (See also: BINARY (digit)).
BINARY (Digit)
A minimum number of digits (old Latin digita meaning fingers) needed to transmit data, illustrated by a 0 (zero) representing OFF and a 1 (one) representing ON.
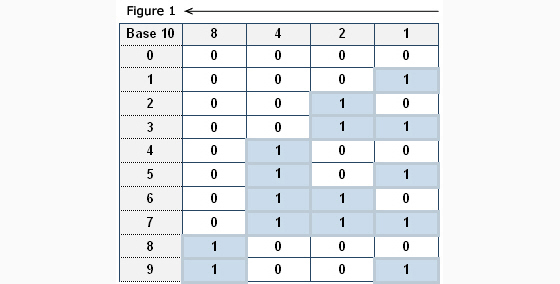
Individually these are called BITs – the B from BINARY and the IT from DIGIT making up the word BIT. Observe the table (Figure 1) below ilustrating 4-BIT (1,2,4,8), the numbering system from right to left across the top doubling from 1 to 2, from 2 to 4 and from 4 to 8.
Combinations of four (4) BITs are known as nibbles; eight (8) BITs a byte (approxmately one character of data); sixteen (16) a word; thirty-two (32) BITs, a long word or dword (double word also used as a term for sixty-four (64) BITs)) and; (one-two-eight) 128 BITs a dqword (double quadruple word (Intel)) / oword (octuple word (Microsoft)).
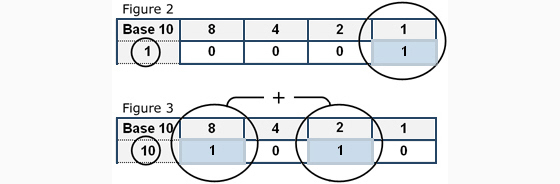
The diagrams above and below illustrate how Binary is converted to Base 10 (Figure 1 (above)) and vice-versa (Figures 2 and 3 (below)).
An ASCII character table (widely published to the web) will give corresponding characters… The ASCII code corresponding with Denary '65' (Base 10 (Decimal)) is 'A' (65=A).
See: Figure 4 below (8-BIT (1,2,4,8,16,32,64,128)), observe that there is a one (1) beneath the Decimal 1 top right, and a one (1) beneath the 64 giving a total of 65 (1+64=65 (the remainder all zero's)).
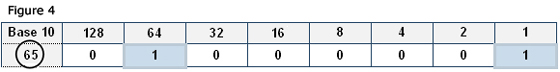
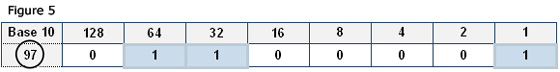
Figure 5 below: (1+32+64=97 (a)).
Summary
Eight BIT: 01000001 = Base ten '65'.
Base ten '65' = ASCII character 'A'.
Eight BIT: 01100001 = Base ten '97'.
Base ten '97' = ASCII character 'a'.
1 to 128 right to left, figures 4 and 5 above, total 255. To achieve decimal 256 to 511, 9-BIT is needed (doubling from 128 to 256). 10-BIT = 512 to 1023; 11-BIT = 1024 to 2047; 12-BIT = 2048 to 4095; 13-BIT = 4096 to 8191; 14-BIT = 8192 to 16383 and so on (See also: Denary).
BIOS
Basic Input / Output System – A microchip containing computer configuration (Initial Setup) data. The BIOS firstly unpacks compressed data from the on-board chip to Random Access Memory (RAM) enabling hard-drive system files to then be loaded into RAM (See also: CMOS).
BIT
See: BINARY (digit).
BIT MAP
Method of displaying on a computer screen, such that each pixel (picture element) corresponds to one or more bits in memory.
BLEED
A printing term, where an illustration or artwork extends beyond/to the edge of a page.
BNC
The Bayonet Neill-Concelman (BNC) connector is a common type of RF connector used with coaxial cable.
BOLD
Bold or Boldface – Emphasis in typography, enhancement to text, increasing the weight of the font, making it stand out more.
BUS
A data connections between two or more devices, a data pathway… The data path on the computer's main board (motherboard) that interconnects the microprocessor and other components. The bus connects the CPU, memory and expansion slots.
BYTE
A byte (8 bits) roughly equates to a character of information. One thousand and twenty-four (1024) bytes corresponding to one kibibyte (See also: BINARY (digit), KIBIBYTE, KILOBYTE, GIGABYTE (GB) & GIBIBYTE (KiB), MEGABYTE and KILO).

CAD (Design)
Computer Aided Design.
CAD (Smart Card)
Card Acceptance Device – A device (usually a point-of-sale terminal) that is capable of reading and processing data from magnetic stripe and chip cards (See also: EMV).
CACHE
Short-term storage – Cache, derived from the French word for a hiding place, is pronounced like 'cash'. A cache is used to speed up certain computer operations by temporarily placing data, or a copy of it, in a location where it can be accessed more rapidly than normal.
Data from a storage disk, for example, may be cached temporarily in high-speed memory so that it can be read and written more quickly than if it had to come directly from the disk itself; or a microprocessor may use an on-board memory cache to store temporary data for use during operations.
CAPTCHA
A type of challenge-response used in computing to help ensure that the response is generated by an individual, not a robot for instance. A common type of CAPTCHA requires the user to enter letters or digits from an image that appears on the screen.
The term 'CAPTCHA' was coined [2000] by Luis von Ahn, Manuel Blum, Nicholas J. Hopper and John Langford (Carnegie Mellon University). It is an acronym based on the word 'capture' that stands for: 'Completely Automated Public Turing test to tell Computers and Humans Apart'.
CARRIAGE RETURN KEY
Key on the right of a standard keyboard and lower right of the numeric keypad (Enter) returning the cursor down a line. For example, having completed paragraph of text (returning twice to leave a line space).
CEO
Chief Executive Officer – The highest-ranking executive in a company or organisation.
CGI
Computer Generated Imagery (See also: GUI).
CHARACTER
A, b, c, or numerical-character for example: 1, 2, 3…
CISC
Complex Instruction Set Computing (See also: RISC).
CLAIT
Computer Literacy and Information Technology.
CMOS
Complimentary Metal Oxide Semi-conductor (See also: BIOS).
CMS
Call Management System.
CMYK
Cyan, Magenta, Yellow and Black (See also: RGB).
COLOSSUS
The first Electronic Programmable Digital Computer [1943-44], developed for use during WWII (2).
COM
Computer Output Microfilm – Computer generated microfilm images.
COMPUTER SPACE
The first video game arcade machine (an arcade version of Space-wars) built by Nolan Bushnell [1971].
CPE (Broadband)
Customer Premises Equipment, e.g. BT Vision Box (See also: LLU).
CPU
The Central Processing Unit, a processor that decodes instructions and converts binary, calculates and governs the speed at which data is transferred; measured in Megahertz (MHz) approximately 1,000,000 bits per second, consisting of the control unit, arithmetic unit, program counter and register (See also: MIPs).
CRT
Cathode Ray Tube [1879] – More recently replaced with Flat Panel (Not Flat Screen) Monitors; Liquid Crystal Displays (LCD (See also: FSP)).
The first real electronic game on a digital computer with a CRT was called Space-wars programmed in 1961 by Steve Russell at the Massachusetts Institute of Technology.
CURSOR
The edit point within a document generally flashing on screen, indicating the position where the data is entered (See also: I-BEAM).
CVS
Computer Vision Syndrome – Computer Induced Eye Strain. One is perhaps more likely to suffer from CVS if they sit continuously for two hours or more in front of a computer.

DATABASE
Data-management program.
DCC (Internet)
Direct Client Connection, a protocol used on IRC to send files between users, create private chats and make a whiteboard for shared drawing (See also: BBS, IRC).
DDR
Double Data Rate – A memory type supporting data transfer on both edges of the clock cycle; working twice as fast as conventional, but now redundant SD-RAM. DDR (184 pin) operates at 266, 333, and 400MHz; DDR2 (240 pin) at 400, 533, 667, 800, 1066MHz; DDR3 (240 pin (Not identical to DDR2)) at 1066, 1333, 1600MHz (See also: BUS).
DEFAULT
Pre-selected, preferred option, e.g. where two or more printers are installed – when printing, the default printer is the pre-selected/preferred device. A default setting for your web browser might be for example: http://www.google.co.uk
To change a default website in Internet Explorer (IE): Open the Internet Browser (IE); Select Tools from the Menu Bar [if not visible by default, select Menu Bar from the Tools drop down menu, top right]; Select Internet Options; Enter your preferred Home page in the text area [General tab] at the head of the Internet Options dialog box.
DEL
Distributed Electronic Learning (Formerly Distance Learning).
DENARY
Base ten (10) – Decimal – the numbering system most common to us (See also: BINARY (digit)).
DEP
Data Execution Prevention (DEP) is a security feature that can help prevent damage to your computer from viruses and other security threats. Harmful programs can try to attack Windows by attempting to run (also known as execute) code from system memory locations reserved for Windows and other authorised programs. These types of attacks can harm your programs and files.
DEP can help protect your computer by monitoring your programs to make sure that they use system memory safely. If DEP notices a program on your computer using memory incorrectly, it closes the program and notifies you (Source: Microsoft).
DES (Smart Card)
Data Encryption Standard – A cryptographic algorithm in which two users share the same secret key. This algorithm is used in VSDC transactions for various functions, such as Online Card Authentication (See also: ARQC, VSDC).
DESCENDER (Typography)
The vertical stem below the baseline in a lower case character set, e.g. g, p, and y (See also: ASCENDER).
DHCP
Dynamic Host Configuration Protocol is a protocol used by networked devices (clients) to obtain various parameters necessary for the clients to operate in an Internet Protocol (IP) network. By using this protocol, system administration workload greatly decreases, and devices can be added to the network with minimal or no manual configurations.
DIMM
Dual Inline Memory Modules (DIMMs) – Perhaps better known as SD-RAM. DIMMs supporting 168 pins replaced SIMMs which originally had 30 and later 72 pins (See also: DDR, SIMM).
DMA
Direct Memory Access – When large amounts of information need to be transferred between a disk drive and a computer's memory, a dedicated chip called a DMA controller or DMac takes charge. This has direct access to the system memory and can perform the transfer much faster than the system micro-processor (CPU).
DMac
See: DMA.
DNS
Domain Name System (The) associates various information with domain names – Most importantly, it serves as the 'phone book' for the Internet by translating human-readable computer hostnames, e.g. www.example.com, into the IP addresses, e.g. 208.77.188.166, that networking equipment needs to deliver information [1983].
DNS also stores other information such as the list of mail exchange servers that accept email for a given domain. In providing a worldwide keyword-based redirection service, the Domain Name System is an essential component of contemporary Internet use (See also: IP, TCP/IP, URL).
DONGLE
More recently a generic term, physical device, parallel or USB, that attaches to a PC's I/O port, adds hardware capabilities such as mobile broadband. Otherwise: a hardware device that plugs into a computer port to measure I/O data rate and troubleshoot problems, or a security hardware device that plugs into the serial or USB port, e.g. copy protection perhaps needed to authorise use of software [1979].
DOS
Disk Operating System, written for IBM PC-compatible computers. Often shorthand for MSDOS (Microsoft Disk Operating System), originally developed by Microsoft for IBM [1981] (See also: IBM).
DRM
Digital Rights Management – Media ownership…
DSL (Broadband)
Digital Subscriber Line (See also: ADSL).
DSLAM (Broadband)
Digital Subscriber Line Access Multiplexer.
DTP
Desktop Publishing: Software package for creating documents, illustrating text and/or graphics (in-house publication), creating brochures, flyers, posters etc.

ECDL
European Computer Driving Licence.
ECP
Extended Capabilities Port – Providing support for CD-ROM and scanner connection to PC's, bidirectional operation and DMA support to increase transfer speed in addition to a number of other features.
EDO
Extended Data Out – Faster than earlier 'Fast Page' memory types (See also: RAM).
EMP (Broadband)
Electromagnetic pulse – A broadband, high-intensity, short-duration burst of electromagnetic energy, potentially coupling with electrical/electronic systems to produce damaging current and voltage surges. Albeit common to a nuclear explosion, the possible effects on computing within a blast radius nonetheless all too clear.
EMV (Smart Card)
Europay, MasterCard, Visa Specifications – Technical specifications developed jointly by Europay International, MasterCard International and Visa International outlining the interaction between chip cards and terminals/CADs to ensure global interoperability (See also: CAD).
ENIAC
Electronic Numerical Integrator and Computer – Incorporating 18,000 valves [1944-45].
EPG
Electronic Programme Guide – TV programme guide on the Internet… BBC, ITV or BT Vision, Sky perhaps!
EPP
Enhanced Parallel Port – An effort by Intel, Xircom, and Zenith Data Systems to define faster and bidirectional data transfer through a PC's parallel port. Mitchell Shnier, Computer Dictionary. www.quecorp.com.
EPS
Encapsulated PostScript – A PostScript file intended to be embedded in another document rather than printed directly. Mitchell Shnier, Computer Dictionary. www.quecorp.com.
ERNIE
Electronic Random Number Indicating Equipment – computer designed in mid 20th Century to randomly select Premium Bond winning numbers [1957].
EULA
End User Licensing Agreement.
EVP
Enhanced Virus Protection – A significant number of viruses exploit flaws located in the code of operating systems and applications using a technique called "Buffer Overflow" that forces computers to execute instructions from malicious code stored in data memory.
In order to prevent the execution of these viruses, AMD has provided a hardware memory protection mechanism on all AMD64 processors that is enabled by Windows® Service Pack 2 (SP2). Once activated by the operating system, this feature can protect desktop, notebooks, workstations and servers all using 8th-generation AMD CPUs.
While it does not protect computers from all kind of viruses, it prevents buffer overflow infections, and is available in both 32 and 64 bit execution mode environments. Clearly the advantages of broadband out-way any disadvantages, Fast Internet nonetheless opens the floodgates to our systems and therefore ongoing (prescription) Internet Security is considered essential, a pre-requisite (See also: TROJAN and VIRUS).

FCU
Forensic Computing Unit – The National Health Service (NHS) Counter Fraud & Security Management Service (CFSMS) Forensic Computing Unit (FCU) provides a comprehensive and professional forensic computing service to recover digital evidence for use in criminal, civil and disciplinary proceedings.
FECs (Broadband)
Forward Error Corrections.
FEPS
Front-end Processors.
FFP
FLOPPY DISK
A removable 'now redundant' disk, more typically 2MB (MiB) with a formatted capacity of 1.44MB [IBM 1971] [Sony 1981]. Global manufacture of the floppy disk has now come to an end March [2011], albeit they are no doubt still available to purchase (See also: Mb and REMOVABLE MEDIA).
FLUFF (Broadband)
Facility for the Upload of Large File Format/Files.
FLUSH
Text that is aligned to one side (See also: ALIGNED, JUSTIFY, and RANGE).
FORMAT
a) Process used to initialise magnetic media – Writing tracks to and preparing a disk for storage. The layout and arrangement of tracks and sectors on magnetic media.
b) The layout of text and/or graphics on a page or screen.
FSP
Flat Screen Panel (See also: LCD).
FTP
File Transfer Protocol – A protocol, means to transfer files (creations, documents etc.) via the Internet, uploading files to server space ready to be viewed or downloaded.
FTR (Broadband)
Fault Threshold Rate.
FTTC (Broadband)
Fibre to the Cabinet.
FTTH (Broadband)
Fibre to the Home.
FTTP (Broadband)

GB
See GIGABYTE (GB) & GIBIBYTE (KiB) below.
GIGABYTE (GB) & GIBIBYTE (GiB)
Gigabyte: prefix indicating a multiple of the unit 'byte', 109, in this context therefore 1 Gigabyte is 1 000 000 000 bytes. However, historically when in computing, one thousand and twenty-four (1024) 103 (1024x1024x1024).
Gibibyte: hard drives are likely sold in Gigabytes (109) or Terabytes (1012), e.g. a capacity of 500GB, i.e. 1000:103 (x500) but nonetheless partitioned in Gibibytes, e.g. a single partition of 488.28GiB, i.e. 1024:103 often referred to as 'Formatted capacity' (Must see: KIBIBYTE (See also: BINARY (digit), BYTE, MEBIBYTE, MEGABYTE and KILO)).
GEM
Graphic Environmental Manager – Early user interface (See also: GUI).
GIF
Graphics Interchange Format – A format developed by CompuServe. Those who have Microsoft Office installed to their workstation may find that their software encompasses an option to custom install Microsoft Photo Editor, supporting this file type, additionally featuring an option to apply transparency to an image (See also: JPEG).
GNOME
Guarding Naturally over Mother Earth – Many GNOME's may feel unwanted and out-of-work as computers replace them, but will undoubtedly continue to watch over us regardless.
GUI
Graphical User Interface – Virtual Desktop, Windows for example (See also: PLATFORM). First developed by Zerox, used for the Apple Macintosh [1973].

HARD DISK
Also known as a hard drive, a sealed unit that stores magnetic data measured in bytes. This form of storage is more convenient, faster and more secure than that say of flash media. Data files of an important nature might be stored to a partition (on the hard drive) or subject to the value placed on data, backed-up to an external drive.
Hard-drive capacity is often wrongly referred to as, or mistaken for memory… See instead: DDR, DIMM, EDO, RAM, SDRAM, SIMM.
HARD DRIVE
HDTV
High Definition Television.
HTML
Hypertext Mark-up Language.
Example
<html>
<head>
<title>Document Title Here</title>
</head>
<body>
<p>Paragraph text goes here…</p>
</body>
</html>
A file such as the one illustrated above can be written in Windows Notepad (Programs/ Accessories); adapted and/or developed to your own liking, saved as an html file (add .htm to the file name when saving, e.g. file.htm). Launch the web file by opening (double-clicking on) the resulting document shortcut (icon)…

I-BEAM
An ![]() shaped pointer replacing the usual symbol (arrowhead pointer) in text processing applications, facilitating improved accuracy when placing between two characters for editing.
shaped pointer replacing the usual symbol (arrowhead pointer) in text processing applications, facilitating improved accuracy when placing between two characters for editing.
IBM
International Business Machines – The deep blue. In 1943, IBM chief Thomas Watson said that there would only ever be enough demand for five computers in the world…
IBT
Integrated Business Technology – Programme following on from Computer Literacy and Information Technology (CLAIT).
ICDL
International Computer Driving Licence.
ICT
Information and Communication Technology – The convergence of Computing, Information Technology (IT), Telecommunications and Data Networking Technologies into a single technology (See also: IET).
IDE
Integrated Drive Electronics – A Hard disk drive with built-in electronics necessary for use on a computer. Also refers to the PC INTERFACE to which disk drives connect.
IEE
Institute of Electrical Engineers.
IET
Information Education Technology – A development of Information Technology (IT (See also: ICT)). Also: The Institution of Engineering and Technology.
INPUT DEVICE
Keyboard, Scanner for example (See also: SELECTION DEVICE).
INTEL
Intel is a US based multinational corporation that is best known for designing and manufacturing microprocessors and specialised integrated circuits [1968] (See also: AMD).
INTER-LINE SPACING
Space between paragraph lines (See also: LEADING and LINE SPACING).
INTERNET
The Internet is a global network connecting millions of computers (See also: LAN, WAN, WWW).
IO
Input Output (I/O).
IP
Internet Protocol – an address of a computer or other network device on a network using IP or TCP/IP (See also: DNS, TCP/IP, URL).
IPS
Instructions per second… See: MIPs
IRC (Internet)
Internet Relay Chat, a chat protocol initially developed as a means of communication utilising a bank of servers known as an IRC network (See also: BBS, DCC).
ISA
Industry Standard Architecture – The original specification for the EXPANSION SLOTS used on the first IBM PC; replaced by its successor – the PCI SLOT. Also: Instruction-Set Architecture, Internet Security and Acceleration, Internet Server Application.
ISDN
Integrated Services Digital Network or Isolated Subscriber Digital Network – An international communications standard that allows ordinary telephone lines to transmit digital instead of analogue signals, allowing data to be transmitted at a faster rate than with a traditional 56K (now redundant) modem (See also: ADSL).
ISO
International Standards Organisation – An international organisation responsible for setting international standards, such as the ISO Latin-1 character set.
ISP
Internet Service Provider – A company that provides access to the Internet.
IT
Short form meaning Information Technology – Concerned with all aspects of managing and processing information (See also: ICT, IET).
ITIL
Information Technology Infrastructure Library – ITIL is best practice in IT Service Management, developed by the Office of Government Commerce (OGC) and supported by publications, qualifications and an international user group.

JAVA
A programming language developed by Sun Microsystems, initially for embedded controllers in consumer electronics – now of course applied to applications widely used across the Internet.
JPEG
Joint Photographic Experts Group – An image (jpg) format giving the user control over the quality and therefore the size (in bytes) of an image. Widely used on the Internet, however not supporting transparency (See also: GIF).
JUSTIFY
Text that is aligned to one side – Fully justified: Text that is aligned to both margins within a document (See also: ALIGNED, FLUSH or RANGE).

KERNEL (Computing)
The kernel is the central component of most computer operating systems – it is a bridge between applications and the actual data processing at hardware level. The kernel's tasks include managing the system's resources (the communication between hardware and software components).
KEYBOARD
Input device for entering text… into a word processing application for example.
KIBIBYTE, or KiB
1,024 bytes (1998 (Must see: KILOBYTE (See also: BINARY (digit), BYTE, KILO, MEBIBYTE and MEGABYTE))).
KILO (Symbol: K)
A prefix indicating a multiple of one thousand (103), as in kilogram. Often when the binary system is used as in computing, it may indicate a multiple of 210, i.e. 1 024 as in kibibyte (Not Kilobyte (Must see: KIBIBYTE and KILOBYTE)).
KILOBYTE, kB or KBYTE
1,000 bytes (Must see: KIBIBYTE (See also: BINARY (digit), BYTE, MEBIBYTE, MEGABYTE and KILO)).

LAN
Local Area Network – A computer network that spans a local area. Most LANs are confined to a single building or group of buildings. However, one LAN can be connected to other LANs over any distance via telephone lines and radio waves. A system of LANs connected in this way is called a Wide Area Network (WAN (See also: 802.11, INTERNET, WAN, WEP)).
LCD
Liquid Crystal Display (Laptop (See also: FSP)).
LEADING
The distance in points (72 points to an inch) between lines of text, believed taken from character sets arranged in lead blocks prior to setting for printing (See also: INTER-LINE SPACING).
LED
Light Emitting Diode.
LEO
Lyons Electronic Office [1951].
LINE LENGTH
The span across the width of a page less the margins, e.g. Width – Margins = Line length.
LINE SPACING
The horizontal space between paragraphs of text, or space allocated to a string of text (See also: INTER-LINE SPACING and LEADING).
LLU (Broadband)
Historically owned and maintained by British Telecom (BT), LLU means that other companies can access the telecoms exchanges, best describes the de-regulation of the former BT exchange network which enables third-party access local to the broadband clients' premises. The 'Local Loop' describes the wires and equipment that connect the client to the local telephone exchange. BT (Openreach) of course take responsibility for and oversee continuity (See also: ADSL, CPE).
LMS

MAC (Broadband)
Migration Authorisation Code.
MAGNETIC MEDIA
Media with a surface made from magnetic material used for data storage – such as a hard drive or floppy disk.
MALVERTISING
The implementing of malware, possibly involving hackers posting malicious adverts on websites, or perhaps simply by way of a compromised browser - if you see double-underlined links to unauthorised advertising pop-ups embedded in this website, for example, then you might want to repair your Internet browser, e.g. IE9; check for Windows updates and fully scan your computer for conceivable intrusions.
MALWARE
Miscellaneous threats include applications that do not fit into other categories, or they fall into multiple categories. These typically include some form of potentially abhorrent functionality that may pose privacy or security risks.
Malicious software (Mal-ware) is designed to infiltrate or damage a computer system without the owner's informed consent – a variety of forms of hostile, intrusive, annoying software or program code.
A Rogue Security Program is software that claims to scan and detect malware or other problems on the computer, but attempts to trick users into purchasing the program by presenting the user with intrusive, deceptive warnings and/or false, misleading scan results. Such programs may use aggressive, deceptive advertising likely installed without notice or consent, often through exploits.
Example of a Malware Trojan or Trojan-based Malware:
TrojanDownloader:ASX/Wimad
Technical Analysis
TrojanDownloader:ASX/Wimad, for example, is a detection for malicious Windows media files that are used in order to encourage users to download and execute arbitrary files on an affected machine. When opened with Windows Media Player, these malicious files open a particular URL in a web browser.
What does this mean?
Simple Analysis
The Trojan (TrojanDownloader:ASX/Wimad (in this example)) exploits, likely installs to your computer through a flaw in the system. The installed Trojan then possibly by way of malicious media files, often received through or associated with peer to peer software, such as Limewire, encourages the download of Malware to your PC, occasionally on a whim (without thought), either automatically or from what may simply look like a known or credible website. The installed Malware will likely then use unwanted, aggressive and misleading scan results to further persuade the user to pay for software to resolve the problem.
PrivacyCenter is one example of a fake anti-virus 'rogue' programme that hijacks and blocks computers; SecurityTool another, not necessarily triggered by a Trojan, possibly gaining access by way of a flaw in a poorly maintained or unstable system; Desktop Security 2010, TotalSecurity and Vista Security are others (See: ADWARE, MALVERTISING, ROGUE SECURITY, ROOTKIT, TROJAN, WORM and VIRUS (See also: VIRUS CLEANING)).
MCOMMERCE
Mobile Commerce, also known as mCommerce or M-Commerce, is the capacity to manage commerce using a mobile device, such as a mobile.
MEBIBYTE, or MiB
1,024 Kibibyte (See also: BINARY (digit), BYTE, KIBIBYTE, KILOBYTE, GIGABYTE (GB) & GIBIBYTE (KiB) and MEGABYTE).
MEGA (Symbol: M)
A prefix indicating a multiple of one million (106 (Base 10)), as in megawatt. When the binary system is used as in computing, it may indicate a multiple of 220 (Binary (See also: BINARY (digit), GIGABYTE (GB) & GIBIBYTE (KiB), MEBIBYTE and MEGABYTE)).
MEGABYTE, MB or MBYTE
1,000 Kilobyte (See also: BINARY (digit), BYTE, GIGABYTE (GB) & GIBIBYTE (KiB), KIBIBYTE, KILOBYTE and MIBIBYTE).
MEMORY
See: RAM (Random Access Memory), DDR, SDRAM.
MCA
Micro Channel Architecture.
MIPs
Millions of Instructions per Second…
Clock pulse = Cycle.
Speed = Cycle time.
CPU = 1 operation per cycle.
1000MHz = 1000 million cycles per second.
1024MHz = 1GHz (1024 million cycles per second).
(See also: CPU and MEGA).

NEPs
Network Equipment Providers.
NETWORK (Computer)
A group of two or more computers linked by cables or wireless signals or both, which can communicate with one another using network protocols. Networks can also include other devices, including printers, routers and network hubs (See also: LAN).
NETWORK FIREWALL
A hardware or software device (or combination of the two), that prevents unauthorised Internet users from gaining access to private networks.
NETWORK HUB
Hardware that connects computers to one another on a local network.
NFC
Near Field Communication (NFC) technology makes life easier and more convenient for consumers around the world by making it simpler to make transactions, exchange digital content and connect electronic devices with a touch. Presently, mobile transactions in the UK are limited to £150.00, '11.
NONE PROPORTIONAL SPACING
Character spacing that does not vary in width – perhaps only used for tables and text processing where work might be illustrated as if produced on a typewriter (See also: PITCH).
NTLDR
NTLDR is the abbreviation of 'NT Loader', the boot loader for all releases of Windows NT (New Technology) operating systems up to and including Windows XP / Windows Server 2003.

OEM
Original Equipment Manufacturer – OEM Licence relating to Software and/or Hardware used in pre-built systems, made available for, or restricted to the Manufacturing or Service Sector.
OEM System Software (Windows XP, Vista, Windows 7) for example, is installed to newly commissioned workstations – OEM Application Software (Internet Security) perhaps if a hardware component such as a hard-drive is replaced.
OGC
Office of Government Commerce (See also: ITIL).
OLAs
Operational Level Agreements (See also: SLAs).
OLED
Organic Light Emitting Diode – Used in thin-screen technology, no back-light required but limited lifespan in the region of 50% that of a normal flat-panel display.
OS
Operating System.
OUTPUT DEVICE
A printer or monitor for example (See also: INPUT DEVICE).
OVERLAY (telephony)
Overlay, Overlay Plan – The practice of introducing a new area code by applying it onto a geographic area that is already occupied by one or more existing area codes, resulting in two or more area codes serving the same area. As the number of lines in use continues to grow in the UK, some areas are close to full capacity. Ofcom at the turn of the millenium signalled a number of areas of concern, not excluding Northampton and Peterborough reaching full capacity by by 2012.

PAC
Porting Authorisation Code – Pre-requisite for keeping a current mobile number when switching from one network to another, e.g. from Vodafone to O2.
PATA
Parallel Advanced Technology Attachment.
PATH
The path followed to arrive at any given file stored to magnetic media (hard disk for example). Where C:\ is the ROOT (start), and a file is archived in a sub-directory within a directory (folder) on the root – then the path would be: C:\Directory\Sub-directory\file.doc. Where the directory is Office and the sub-directory is Word – then the path would be: C:\Office\Word\file.doc (See also: BUS).
PCI
Peripheral Component Interconnect.
PCP
PDA
Personal Digital Assistant – A pocket-sized computer typically operated via a touch-screen stylus rather than a keyboard.
PHABLET
A Phablet is a smartphone hybrid best describing devices with a screen between 5.0 to 7.0 inches in size, designed to straddle the functionality of a smartphone and tablet, purging the need for two devices.
PHARMING
Pharming is an attempt to obtain personal or private information (most often financial-related) from Internet surfers by hijacking a domain name or URL, then redirecting users to an imposter website, where fraudulent requests for private information are made (Source: Symantec).
PHISHING
A means to fool recipients into divulging personal financial data such as credit card numbers, account usernames and passwords, social security numbers, etc. by way of 'spoofed' e-mails and 'fraudulent' websites. Hijacking trusted brands of well-known banks, credit card, money holding companies and online retailers, phishers are able to convince perhaps as many as 5% of recipients to respond.
Email may take the form of advice, and such emails are likely to include a fake link possibly adding to its apparent authenticity – Note the address behind the link – Also be warned, this is not banking practice – Do not divulge confidential information of this nature through any online system, your bank will not ask you to input a complete password or direct you to a site where they ask you to input passwords to update their records. If in doubt you might contact your money managers more directly (Must see also: PHARMING, WORM).
PHREAKING
Phreaking is a term coined to describe the activity of people who study, experiment with or explore telecommunication systems, such as equipment and systems connected to public telephone networks. More recently, phreaking has become closely linked with computer and/or telecoms hacking. This is sometimes referred to as the H/P culture (the H for hacking and P for phreaking (Must see also: PHARMING, PHISHING (Source: Wikipedia))).
PITCH
The measure of horizontal character spacing taken from PER INCH – Where the horizontal width is the same regardless of character, e.g. an ' M ' or an ' I ' (See also: NONE PROPORTIONAL SPACING).
PLATFORM
System software – Windows for example, the launch pad (interface) for application software such as Microsoft Word (See also: WINDOWS).
PNRP
PeerName Resolution Protocol – Peer to Peer Network Protocol.
POP3
Post Office Protocol 3 – A protocol used to retrieve e-mail from a remote server over an Internet connection.
POST
Power-on Self Test – A test sequence that runs when a computer is switched on.
POST Probe – A means to probe (Test) hardware by running a series of tests when a computer is switched on.
PPC (Internet Marketing)
Pay Per Click (See also: SEO).
PROPORTIONAL SPACING
Horizontal character spacing in proportion to size, e.g. an M would be allocated more space than an I – Not un-typical of all modern applications. Good reason to use the tab key perhaps, not the space bar (See also: NONE PROPORTIONAL SPACING and TAB (TAB KEY)).
PROTECTED SPACE
Replacing a normal space between two related words, to ensure that they word wrap together. This can be achieved in Ms Word and Publisher by holding both the Shift and Ctrl key when pressing the space bar. And is written as: in HTML, e.g. word wrap (See also: WRAP TEXT).
PSTN
Public Switched Telephone Network (See also: ADSL, STD).

QWERTY
The six alphabetical characters upper left of a standard keyboard giving name to the 'QWERTY' Keyboard.

RAM
Random Access Memory (See: DDR, DIMM, EDO, SDRAM, SIMM).
RANGE
Text that is aligned to one side (See also: ALIGNED, FLUSH and/or JUSTIFY).
RANSOMWARE
See: ROGUE SECURITY.
RASPBERRY Pi
The Raspberry Pi is a Small-board (credit-card sized) Computer; the model B first available in the UK from 29 February [2012] (See: ARM, SBC, RISC (See also: http://computerspace.co.uk)).
REMOVABLE MEDIA
Such as a floppy or zip disk, compact disc (R/RW), DVD (R/RW (DL (Dual-Layer))) or external hard-drive facilitating backing-up (safeguarding), or convenient transfer of data (CV, Music, Photogrpahs etc.) from one workstation to another (See also: FLOPPY DISK).
REN
Ring Equivalent Number – You should see this on the underside of your telephone, e.g. REN=1. A telephone/broadband line typically has a maximum REN of four (4), i.e. the line can operate up to four telephone accessories (e.g. answer phone, fax, modem), each with a REN of one (1).
A telephone line needing to support a REN greater than four may need to be *boosted, however this might lead to unwanted interference if the line is also supporting broadband, and one therefore should perhaps consider a dedicated filtered broadband master socket (BT ADSL V10 or equivalent (No filter required)). Otherwise, all sockets on the ADSL broadband line accommodating equipment must be filtered, and no one device should pass through more than one ADSL filter.
*Broadband: In tests the BT I-Plate (iPlate) however, has been shown to boost line speeds – typically by 1.5Mbps, though this may not be worthwhile where internal wiring is low frequency, i.e. telephone extensions, old telecom cable initially intended only for telephone, not broadband.
RFID (Broadband)
Radio Frequency Identification.
RFS (Broadband)
Ready for Service, e.g. BT Infinity.
RGB
Red, Green and Blue (See also: CMYK).
RISC
Reduced Instruction Set Computing (See also: ARM, CISC, RASPBERRY Pi, SBC).
ROAMING
Use of mobile device outside natural borders, e.g. phone tariff while overseas.
Update 2016
When you travel to a foreign country with your mobile phone, you are roaming - your mobile phone company and one in the foreign country work together to keep you connected, so you can make and receive mobile phone calls, write text messages, surf the Web and download content. These roaming charges will cease to exist in the EU as of 15 June 2017 (Source: European Commission).
ROGUE SECURITY/ROGUE SOFTWARE
Rogue Security – PrivacyCenter is one example of a fake anti-virus 'rogue' programme that hijacks and blocks computers; SecurityTool another, not necessarily triggered by a Trojan, possibly gaining access by way of a flaw in a poorly maintained or unstable system; Desktop Security 2010, TotalSecurity and Vista Security are others. Fake results might typically report software issues, though increasingly more versions may either integrate with or clone anti-virus applications, and/or simulate hardware, registry or system problems.
Other rogue type instrusions/scams might include fake police warnings or 'ransomware' (also know as the United Kingdom Police virus or Police Central e-crime Unit virus or UKash Scam) suggesting 'illegal activity', locking the PC, e.g. Metropolitan, Yorkshire Police etc. prompting the user to pay a fine by way of of UKash. It's likely ransomware exploits Java or Flash vulnerabilities to load the malicious code on to a system.
More misleading/rogue applications
Antivirus2009
AntiVirusXP2008
SpySheriff
System Tool
TheRegistrySentinel
VirusDoctor
VirusRemover2008
Vista Antivirus 2012 (May require a full recovery to remove from system)
Windows XP Repair
WindowsDiagnostic
WiniGuard
Must see: MALWARE, WORM
ROM
Read Only Memory (See also: CMOS).
ROOTKIT
A rootkit is software that enables continued access to a computer while actively hiding its presence from administrators. Although rootkits can serve a variety of ends, they have gained notoriety as malware, hiding applications that appropriate computing resources or steal passwords without the knowledge of administrators and users of affected systems (Must see: MALWARE).
RSS (File Format)
Really Simple Syndication, Rich Site Summary or RDF Site Summary, several similar forms of web syndication used by news websites and weblogs.

SAPI
Speech Application Programming Interface (See also: API).
SATA
Serial Advanced Technology Attachment.
SBC
Single-board Computer (See: ARM, RASPBERRY Pi, RISC (See also: computerspace.co.uk)).
SELECTION DEVICE
Mouse, trackball for example (See also: INPUT DEVICE).
SDRAM
Synchronous Dynamic Random Access Memory – SDRAM is a redundant memory type replaced by DDR but still found in some computers. SDRAM operates at 66, 100 or 133 MHz bandwidth (See also: DDR, DIMM, RAM).
SEDs
SEO (Internet Marketing)
Search Engine Optimisation (See also: PPC).
sIFR
Scalable Inman Flash Replacement is a technology that allows you to replace text elements on screen with Flash equivalents. sIFR allows website headings, pull-quotes and other elements to be styled in whatever font the designer chooses without the user having it installed on their machine.
SIMM
Single Inline Memory Module – An obsolete memory standard, no longer widely available and rarely found in older PCs. SIMMs had 30 and later 72 pin connectors, and unlike more recent memory types, had to be fitted in pairs (See also: DIMM).
SLAs
Service Level Agreements – An agreement between Customer and their Supplier, part of the IT culture but not universally accepted (See also: CMS, ITIL, OLAs).
SMS
Short Message Service [1992].
SNR (Broadband)
Signal to Noise Ratio.
SNRM (Broadband)
Signal to Noise Ratio Margin.
SOHO
Small Office Home Office.
SPYWARE
Computer software that is installed surreptitiously on a personal computer to intercept or take partial control over the user's interaction with the computer, without the users' informed consent. Must see also: ADWARE and MALWARE (See also: EVP, PHISHING, TROJAN, VIRUS and WORM).
SSA
Software Security Assurance.
SSFP
Service Specific Front Plate.
SSID (Broadband)
Service Set IDentifier – The SSID enables communication between users and the Access Point. The Service Set Identifier is in essence an identity, a unique label given to a wireless Gateway, the broadband router (Access Point). The SSID does not provide any security, can be viewed by anyone within the signal area, is merely the default or chosen tag, e.g. virgin boadband; my place; my router (Must see also: WEP).
SSL (Broadband)
Secure Sockets Layer – An SSL certificate proves your identity and scrambles information sent across the Internet, so nobody else can see it.
SSVC
The Services Sound and Vision Corporation (SSVC), formerly the Services Kinema Corporation (SKC).
STD
Subscriber Trunk Dialling [Dial-up] (See also: ADSL, PSTN).
STRING
Two or more words – together they form a string.
SVGA
Super Video Graphics Array – A graphics standard for PC's providing a resolution of 800 x 600 or higher (See also: VGA).

TAB
Tab, as in filing – A, B, C… etc. A folder/selection option in a Windows environment dialog box, usually across the top (See also: TAB KEY).
TAB KEY
Key above the Caps Lock on the left hand side of a standard keyboard which places the cursor at a default or pre-defined position, usually every 1.27cm or half an Inch from the left margin, perhaps where text is to be inset, or requires arranging in a column format, numerical data for example.
TARDIS (Fiction/Film)
Time and Relative Dimension in Space – A time machine, science fiction television programme Doctor Who.
TCP/IP
Transmission Control Protocol/Internet Protocol – basic communication language or protocol of the Internet. All computers with direct access to the Internet has as a copy of TCP/IP (See also: DNS, IP).
TEXT-WRAP
A desktop and word processing feature facilitating text flow around an image (See also: WRAP TEXT).
TKIP (Broadband)
Temporal Key Integrity Protocol – An encryption protocol included as part of the IEEE 802.11i standard for wireless LANs (WLANs). Now superseded, it was designed to provide more secure encryption than the weaker Wired Equivalent Privacy (WEP), the original WLAN security protocol. TKIP was the encryption method used in WiFi Protected Access (WPA), which replaced WEP in WLAN products (See also: 802.11, WiFi, WPA).
TROJAN
The impact of a Trojan may vary from simply a nuisance factor, theft of confidential information, to the more destructive, leading to instability, reinforcing a need for essential ongoing (subscribed) preventative solutions such as a comprehensive Internet Security package. Trojans are also found linked to Rogue Security (Must see also: MALWARE, ROGUE SECURITY, VIRUS and WORM).
Update 2016
Unlike viruses, trojans do not self-replicate. They are spread manually, often under the premise that they are beneficial or wanted. The most common installation methods involve system or security exploitation, and unsuspecting users manually executing unknown programs. Distribution channels include email, malicious or hacked web pages, Internet Relay Chat (IRC), peer-to-peer networks, etc (Source: Symantec).

UMA
Unified Memory Architecture.
UNSPSC (UN/SPSC)
United Nations Standard Product and Service Code – A single global classification system set by the United Nations for fixing and optimising large volumes of company data, allowing that company to classify the products and services that they buy and sell.
URL
Uniform Resource Locator, or Unique Resource Locator – The addressing format used by web browsers, e.g. http://www.computerspace.co.uk (See also: DNS, IP, TCP/IP).
USB
Universal Serial Bus – A relatively new and widely accepted standard for connecting up to 127 physical devices to a PC.
USB2
Universal Serial Bus 2 – As for USB, but 40 times faster.
USB3
Universal Serial Bus 3 – As for USB2, but 4 times faster.

VDU
Visual Display Unit.
VDSL (Broadband)
Very high speed Digital Subscriber Line (See also: ADSL).
VGA
Video Graphics Array – A graphics standard for PC's providing a resolution of 640 x 480 (See also: SVGA).
VIN (Transport)
The Vehicle Identification Number (VIN) is a unique number to identify a vehicle, regardless of number plate changes. If not matched to the VIN on the database, the number should be verified online before one purchases the vehicle in order to invoke Data Insurance cover. The VIN is normally a mixture of 17 letters and numbers, and does not contain letters I or O, but does contain the numbers one (1) and zero (0) (See: AA CHECK, DVLA ADVICE).
VIRUS
A self-replicating 'malicious' program. A term often used, misused to describe all types of threats, but nonetheless requires interaction from (is triggered by) the user (Must see also: ADWARE, MALWARE, PHISHING, TROJAN and WORM.
VIS (Smart Card)
Visa Integrated Circuit Card Specification – Visa's implementation of the EMV specifications to aid vendors in developing VSDC cards and terminals (See also: EMV, VSDC).
VSDC (Smart Card)
Visa Smart Debit/Credit – The Visa service offerings for chip-based debit and credit programs. These services, based on EMV and VIS specifications, are supported by VisaNet processing, as well as by Visa rules and regulations. The term VSDC is also used to refer to the actual payment application/applet that resides on the card (See also: APPLET, EMV, VIS).

WAE (Legislation)
Web Accessibility Essentials – Equality Act 2010.
WAN (Broadband)
A computer network that spans a relatively large geographical area – Typically, a WAN consists of two or more Local Area Networks (LANs (See also: 802.11, INTERNET, LAN, WWW)).
WEEED
WEEE Directive [2007] – Waste Electronic and Electrical Equipment Directive (WEEED) was to be enforced in the UK and throughout the EC circa 13 August 04, was finally rolled out in January 2007. The directive was written to reduce the waste arising from electrical and electronic equipment, and to improve the environmental performance of those involved in the lifecycle of electrical and electronic equipment. IT and Telecoms Equipment is covered by Category 3 WEEE.
WEP (Broadband)
Wired Equivalent Privacy – A security protocol for wireless Local Area Networks (WLANs) defined in the 802.11b standard. WEP is designed to provide the same level of security as a wired LAN.
However, a much older protocol than WPA, the default setting of some devices may nonetheless be WEP because older wireless devices are not compatible with stronger encryption types, such as WPA (See also: 802.11, LAN, WiFi, WPA).
WHITESPACE
Area left blank in a publication, common in DTP models – Too much white space may be unacceptable, however a frame of white around text can enhance appearance.
WHITESPACE (Typography)
In computer science, whitespace is any single character or series of characters that represents horizontal or vertical space in typography…
WiFi (Broadband)
Wireless Fidelity – The WiFi (Wi-Fi) Alliance is an industry alliance to promote wireless networking arrangements based on the IEEE 802.11 specification. Products approved by the Alliance receive the WiFi certified seal of interoperability (See also: 802.11, WPA).
WINDOWS
Microsoft Windows Operating System:
Windows 3.1; Windows '95; Windows '98 (FE (First Edition), SE (Second Edition)), sometimes referred to as 9X; Windows NT4 and 2000 developed for networks; Windows ME (Millennium Edition); Windows XP (Home), and XP (Professional), Windows Vista (Basic, Premium, Professional and Ultimate (32 and 64bit)); Windows 7; Windows 8. Generations: 1) 3.11, 2) '95, 3) '98, 4) ME, 5) XP, 6) Vista, 7) Windows 7, 8) Windows 8, 8a) Windows 8.1.
WIP
Work In Progress…
WOPR (Fiction/Film)
War Operation Planned Response, from the film WarGames (War Games), 1983, starring Matthew Broderick and Dabney Coleman. A computer whizz-kid taps into the government early-warning system and nearly starts World War III.
WORM
Write Once Read Many – A hoax or virus-like threat likely to trigger a chain reaction; chain mail leading to server overload. This may be automated or might simply encourage an excessive spread of electronic mail using scare tactics, ironic 'false' warning of malicious threats for example, perhaps claiming to be from a known source such as an Internet Security Software House.
Currency
The name, adapted from 'The Shockwave Rider', a science fiction novel, has also come to refer to a malicious program that can copy and propagate itself over the Internet using email programs or other transport tools. A WORM may compromise the security of an infected computer or cause system and data damage (Source: Symantec (Must see also: MALWARE, PHARMING, PHISHING, TROJAN and VIRUS)).
WPA (Broadband)
WiFi Protected Access – Encryption by default to protect the data that moves across the radio waves from it to other wireless devices (Must see also: WEP).
WPA-PSK (Broadband)
WiFi Protected Access-Pre-Shared Key – A simplified but nonetheless powerful form of WPA, most suitable for home wireless networking (See also: SSID, TKIP, WEP, WPA).
WRAP TEXT
Where transcript automatically wraps at the end of a line of text omitting the need to press the return key until the end of a paragraph – a feature of word processors unlike a manual typewriter (See also: PROTECTED SPACE and TEXT-WRAP).
WWW
The World Wide Web is a collection of documents, e.g. web pages, published to the Internet – conceived by Sir Timothy (Tim) John Berners-Lee (British Scientist [1989]) – the Internet is a global network connecting millions of computers (See also: WAN).
WYSIWYG
What You See Is What You Get – Effect or screen display…

XGA
Extended Graphics Adapter – Rarely used term for resolution of 1024 x 768 (See also: VGA and SVGA).

YAHOO
Yet Another Hierarchical Officious Oracle – A widely popular search engine founded by two students from Stanford University [1994].

ZIF
Zero Insertion Force – A socket used for fitting a processor to a printed circuit (main-board) board, utilising a lever to lock the pins into place. A ZIF 7 socket, for example, would support an IBM, Cyrix or AMD K6 2 processor.
ZIGBEE
A low-cost, low-power, wireless mesh networking standard, based upon the IEEE 802.15.4 – 2006 standard for personal area networks (WPAN). The technology is intended to be simpler and cheaper than other WPANs such as Bluetooth with much lower power requirements.
The cost advantage allows Zigbee to be widely deployed in wireless control, monitoring and tracking applications, where its low power-usage allows longer life with smaller batteries, and mesh networking provides higher reliability and longer range.



